[TOC]
一、RBAC介绍
1.1 RBAC简介
RBAC是基于角色的访问控制(Role-Based Access Control )在 RBAC 中,权限与角色相关联,用户通过成为适当角色的成员而得到这些角色的权限。这就极大地简化了权限的管理。这样管理都是层级相互依赖的,权限赋予给角色,而把角色又赋予用户,这样的权限设计很清楚,管理起来很方便。
在RBAC模型里面,有3个基础组成部分,分别是:用户、角色和权限。
RBAC通过定义角色的权限,并对用户授予某个角色从而来控制用户的权限,实现了用户和权限的逻辑分离,极大地方便了权限的管理,在讲解之前,先介绍一些名词:
User(用户):每个用户都有唯一的UID识别,并被授予不同的角色
Role(角色):不同角色具有不同的权限
Permission(权限):访问权限
用户-角色映射:用户和角色之间的映射关系
角色-权限映射:角色和权限之间的映射
1.2 权限管理
只要有用户参与的系统一般都要有权限管理,权限管理实现对用户访问系统的控制,按照安全规则或者安全策略控制用户可以访问而且只能访问自己被授权的资源。
权限管理包括用户认证和授权两部分。
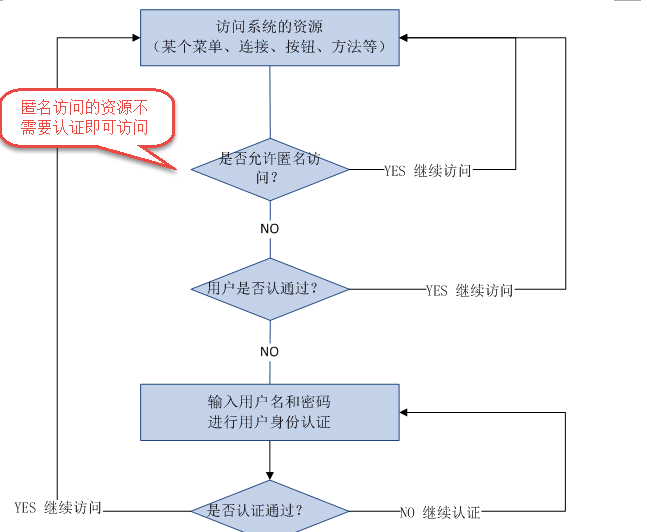
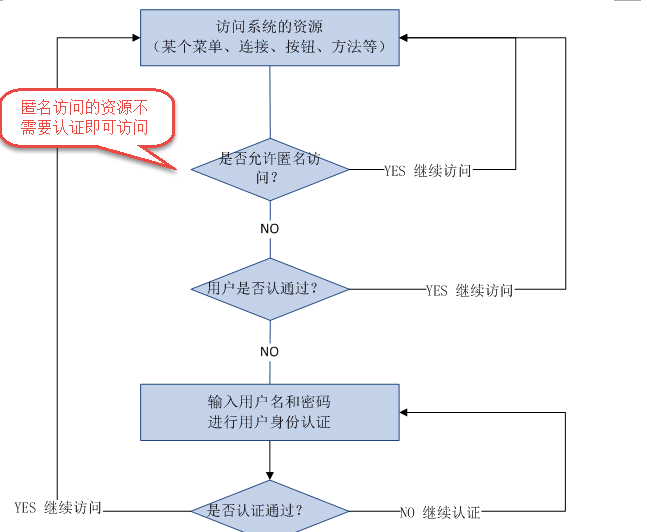
二、 用户认证
用户认证,用户去访问系统,系统要验证用户身份的合法性。最常用的用户身份验证的方法:
1、用户名密码方式、2、指纹打卡机、3、基于证书验证方法。。系统验证用户身份合法,用户方可访问系统的资源。
关键对象:
subject:主体,理解为用户,可能是程序,都要去访问系统的资源,系统需要对subject进行身份认证。
principal:身份信息,通常是唯一的,一个主体还有多个身份信息,但是都有一个主身份信息(primary principal)
credential:凭证信息,可以是密码 、证书、指纹。
总结:主体在进行身份认证时需要提供身份信息和凭证信息。
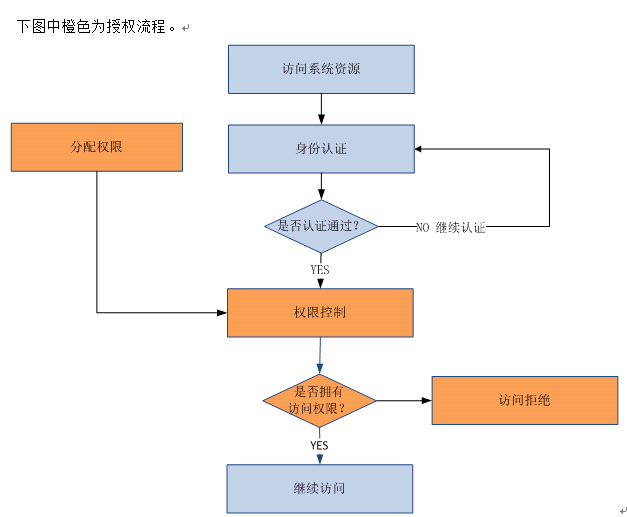
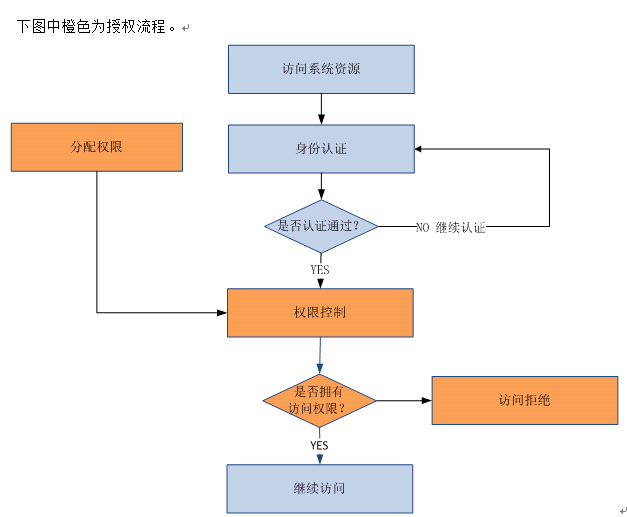
三、用户授权
用户授权,简单理解为访问控制,在用户认证通过后,系统对用户访问资源进行控制,用户具有资源的访问权限方可访问。
关键对象
授权的过程理解为:who对what(which)进行how操作。
who:主体即subject,subject在认证通过后系统进行访问控制。
what(which):资源(Resource),subject必须具备资源的访问权限才可访问该 资源。资源比如:系统用户列表页面、商品修改菜单、商品id为001的商品信息。
资源分为资源类型和资源实例:
系统的用户信息就是资源类型,相当于java类。
系统中id为001的用户就是资源实例,相当于new的java对象。
how:权限/许可(permission) ,针对资源的权限或许可,subject具有permission访问资源,如何访问/操作需要定义permission,权限比如:用户添加、用户修改、商品删除。
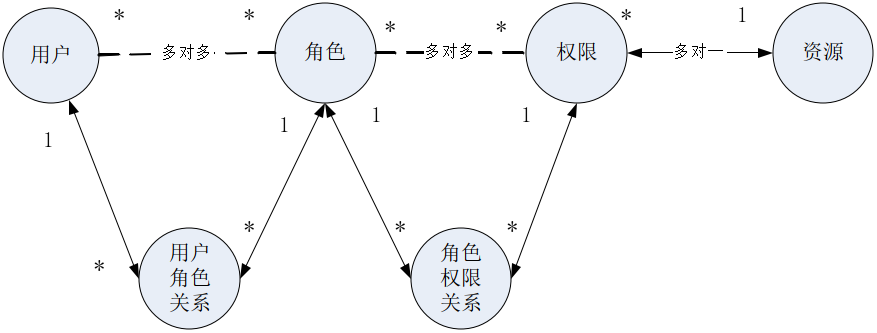
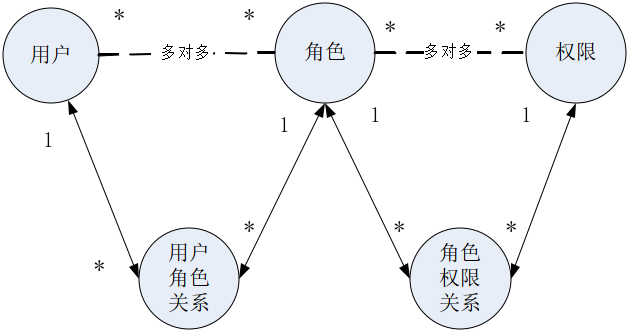
四、权限模型
主体(账号、密码)
角色(角色名称)
权限(权限名称、资源id)
主体和角色关系(主体id、角色id)
角色和权限关系(角色id、权限id)
资源(资源名称、访问地址)
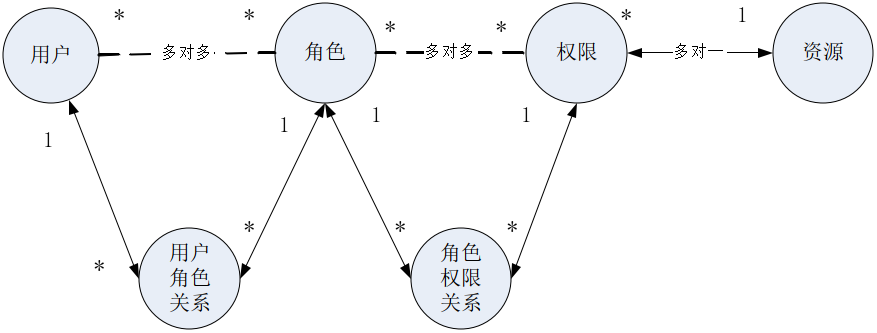
通常企业开发中将资源和权限表合并为一张权限表,如下:
资源(资源名称、访问地址)
权限(权限名称、资源id)
合并为:权限(权限名称、资源名称、资源访问地址)
上图常被称为权限管理的通用模型,不过企业在开发中根据系统自身的特点还会对上图进行修改,但是用户、角色、权限、用户角色关系、角色权限关系是需要去理解的。
分配权限:用户需要分配相应的权限才可访问相应的资源。权限是对于资源的操作许可,通常给用户分配资源权限需要将权限信息持久化,比如存储在关系数据库中,把用户信息、权限管理、用户分配的权限信息写到数据库(权限数据模型)。
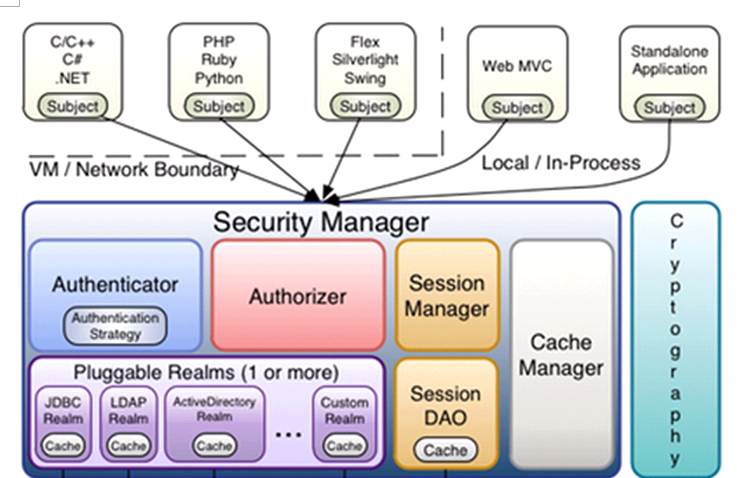
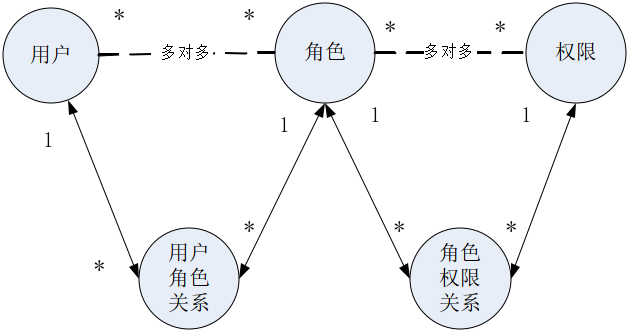
五、Shiro介绍
shiro是apache的一个开源框架,是一个权限管理的框架,实现 用户认证、用户授权,功能强大、且 简单、灵活,且不跟任何的框架或者容器绑定,可以独立运行。
spring中有spring security (原名Acegi),是一个权限框架,使用起来很方便,和spring依赖过于紧密。
subject:主体,可以是用户也可以是程序,主体要访问系统,系统需要对主体进行认证、授权。
securityManager:安全管理器,主体进行认证和授权都是通过securityManager进行。
authenticator:认证器,主体进行认证最终通过authenticator进行的。
authorizer:授权器,主体进行授权最终通过authorizer进行的。
sessionManager:web应用中一般是用web容器对session进行管理,shiro也提供一套session管理的方式。
SessionDao:通过SessionDao管理session数据,针对个性化的session数据存储需要使用sessionDao。
cache Manager:缓存管理器,主要对session和授权数据进行缓存,比如将授权数据通过cacheManager进行缓存管理,和ehcache整合对缓存数据进行管理。
realm:域,领域,相当于数据源,通过realm存取认证、授权相关数据。
注:在realm中存储授权和认证的逻辑。
cryptography:密码管理,提供了一套加密/解密的组件,方便开发。比如提供常用的散列、加/解密等功能。
比如:md5信息摘要算法。
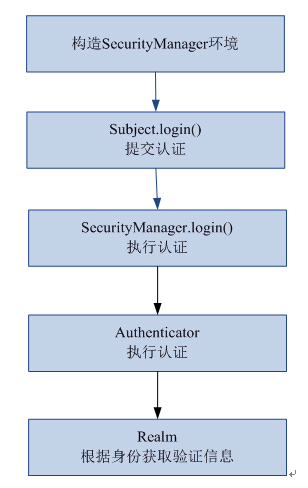
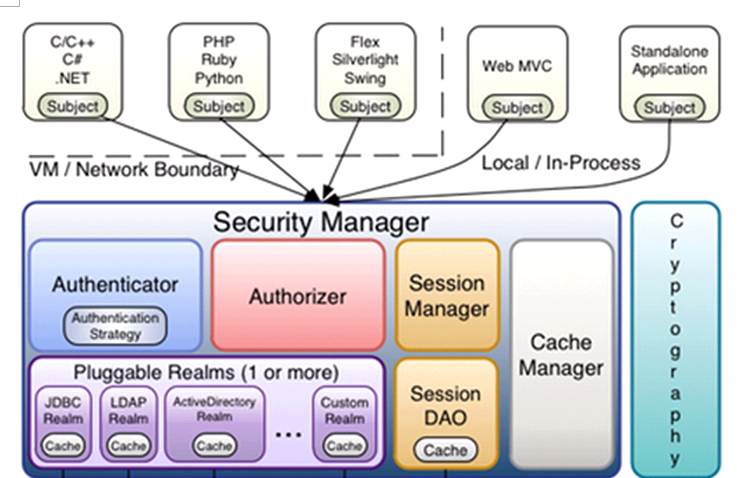
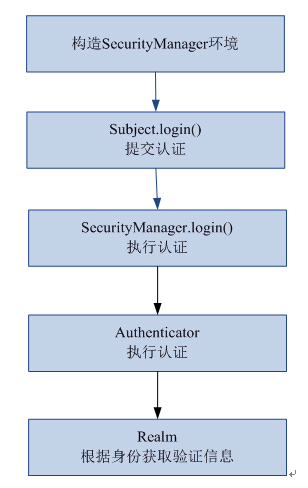
六、认证流程
6.1 创建Maven工程并导入依赖
1
2
3
4
5
6
7
8
9
10
11
12
| <dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.8.0</version>
</dependency>
|
6.2 在resources目录下创建shiro.ini文件,IEDA需要安装*.ini并重启方可生效
1
2
3
4
5
|
[users]
jack=123
tom=456
|
6.3 创建认证测试类
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
| package com.couture.authentication;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.config.IniSecurityManagerFactory;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.subject.Subject;
import org.apache.shiro.util.Factory;
import org.junit.Test;
public class AuthenticationDemo {
@Test
public void testLoginAndLogout() {
Factory<SecurityManager> factory = new IniSecurityManagerFactory(
"classpath:shiro.ini");
SecurityManager securityManager = factory.getInstance();
SecurityUtils.setSecurityManager(securityManager);
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken("jack", "123");
subject.login(token);
boolean isAuthenticated = subject.isAuthenticated();
System.out.println("是否认证通过:" + isAuthenticated);
subject.logout();
isAuthenticated = subject.isAuthenticated();
System.out.println("是否认证通过:" + isAuthenticated);
}
}
|
6.4 执行流程
1、通过ini配置文件创建securityManager
2、调用subject.login方法主体提交认证,提交的token
3、securityManager进行认证,securityManager最终由ModularRealmAuthenticator进行认证。
4、ModularRealmAuthenticator调用IniRealm(给realm传入token) 去ini配置文件中查询用户信息
5、IniRealm根据输入的token(UsernamePasswordToken)从 shiro.ini查询用户信息,根据账号查询用户信息 (账号和密码)
如果查询到用户信息,就给ModularRealmAuthenticator返回用户信息(账号和密码)
如果查询不到,就给ModularRealmAuthenticator返回null
6、ModularRealmAuthenticator接收IniRealm返回Authentication认证信息
如果返回的认证信息是null,ModularRealmAuthenticator抛出异常
(org.apache.shiro.authc.UnknownAccountException)
如果返回的认证信息不是null(说明inirealm找到了用户),对IniRealm返回用户密码 (在ini文件中存在)
和 token中的密码 进行对比,如果不一致抛出异常
(org.apache.shiro.authc.IncorrectCredentialsException)
6.5 总结
ModularRealmAuthenticator作用是进行认证,需要调用realm来查询用户信息(在数据库中存在用户信息)并且进行密码对比(认证过程)
realm:需要根据token中的身份信息去查询数据库(入门程序使用ini配置文件),如果查到用户返回认证信息,如果查询不到返回null
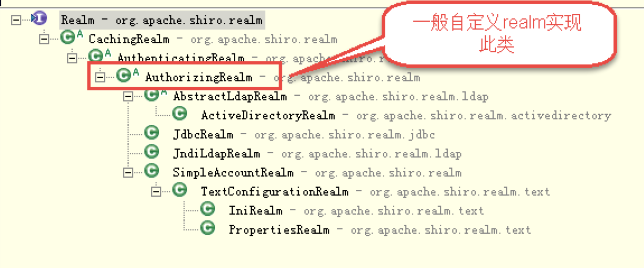
七、使用realm认证
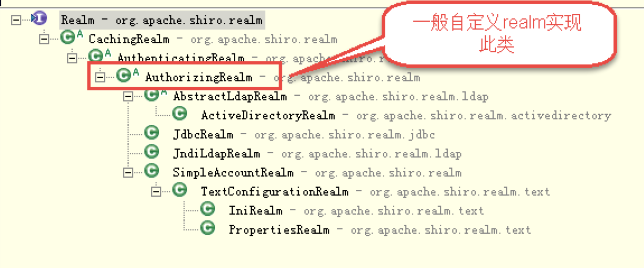
7.1 创建自定义realm
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
| package com.couture.realm;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.SimpleAuthenticationInfo;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
public class realmDemo extends AuthorizingRealm {
private String realmName = "realmDemo";
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken
authenticationToken) throws AuthenticationException {
String principal = (String)authenticationToken.getPrincipal();
System.out.println(principal);
Object credentials = authenticationToken.getCredentials();
String password = new String((char[]) credentials);
System.out.println(password);
if("jack".equals(principal) && "123".equals(password)){
SimpleAuthenticationInfo simpleAuthenticationInfo = new SimpleAuthenticationInfo(principal,password,realmName);
return simpleAuthenticationInfo;
}
return null;
}
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
return null;
}
}
|
7.2 在resource目录下创建shiro-realm.ini(注意:realm路径别配置错了)
1
2
3
4
5
| [main]
realmDemo=com.qf.realm.realmDemo
securityManager.realms=$realmDemo
|
7.3 在AuthenticationDemo类中添加方法进行测试
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
|
@Test
public void testRealmDemo() {
Factory<SecurityManager> factory = new IniSecurityManagerFactory(
"classpath:shiro-realm.ini");
SecurityManager securityManager = factory.getInstance();
SecurityUtils.setSecurityManager(securityManager);
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken("jack", "123");
try {
subject.login(token);
} catch (AuthenticationException e) {
e.printStackTrace();
}
boolean isAuthenticated = subject.isAuthenticated();
System.out.println("是否认证通过:" + isAuthenticated);
}
|
访问controller测试即可
八、MD5加密
通常需要对密码 进行散列,常用的有MD5、SHA,
对MD5密码,如果知道散列后的值可以通过穷举算法,得到md5密码对应的明文(指加密前的密码)。
建议对MD5进行散列时加salt(盐),进行加密相当于对原始密码+盐进行散列。
正常使用时散列方法:
在程序中对原始密码+盐进行散列,将散列值存储到数据库中,并且还要将盐也要存储在数据库中。
如果进行密码对比时,使用相同方法,将原始密码+盐进行散列,进行比对。
8.1.创建MD5Demo测试类,进行测试
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
| import org.apache.shiro.crypto.hash.Md5Hash;
import org.apache.shiro.crypto.hash.SimpleHash;
public class MD5Demo {
public static void main(String[] args) {
String password = "123";
String salt = "abcde";
int hashIterations = 2;
Md5Hash md5Hash = new Md5Hash(password, salt, hashIterations);
String password_md5 = md5Hash.toString();
System.out.println(password_md5);
SimpleHash simpleHash = new SimpleHash("md5", password, salt,
hashIterations);
System.out.println(simpleHash.toString());
}
}
|
8.2在AuthenticationDemo类中添加方法进行测试
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
|
@Test
public void testMD5() {
Factory<SecurityManager> factory =
new IniSecurityManagerFactory("classpath:shiro-realm-md5.ini");
SecurityManager securityManager = factory.getInstance();
SecurityUtils.setSecurityManager(securityManager);
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken("jack", "123");
try {
subject.login(token);
} catch (AuthenticationException e) {
e.printStackTrace();
}
boolean isAuthenticated = subject.isAuthenticated();
System.out.println("是否认证通过:" + isAuthenticated);
}
|
8.3创建shiro-realm-md5.ini
1
2
3
4
5
| [main]
realmDemo=com.qf.realm.realmDemoMD5
securityManager.realms=$realmDemo
|
8.4创建realmMD5
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
| package com.couture.realm;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.SimpleAuthenticationInfo;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.crypto.hash.Md5Hash;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
public class realmDemoMD5 extends AuthorizingRealm {
private String realmName = "realmDemoMD5";
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
String principal = (String)authenticationToken.getPrincipal();
Object credentials = authenticationToken.getCredentials();
String password = new String((char[]) credentials);
System.out.println(password);
Md5Hash md5Hash = new Md5Hash(password, "abcde", 2);
String password_md5 = md5Hash.toString();
System.out.println(password_md5);
String dbpassword = "6585096f3f6735025449cfb351c8cff9";
if("jack".equals(principal) &&password_md5.equals(dbpassword)){
SimpleAuthenticationInfo
simpleAuthenticationInfo = new SimpleAuthenticationInfo(principal,password,realmName);
return simpleAuthenticationInfo;
}
return null;
}
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
return null;
}
}
|
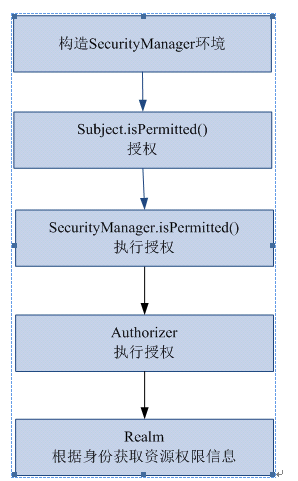
九、授权流程
9.1创建shiro-permission.ini(shiro-permission.ini里边的内容相当于在数据库)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
[users]
jack=123,role1,role2
tom=456,role2
[roles]
role1=user:create,user:update
role2=user:create,user:delete
role3=user:query
|
9.2创建AuthorizationDemo
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
| package com.couture.authorization;
import java.util.Arrays;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.config.IniSecurityManagerFactory;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.subject.Subject;
import org.apache.shiro.util.Factory;
import org.junit.Test;
public class AuthorizationDemo {
@Test
public void testAuthorization() {
Factory<SecurityManager> factory = new IniSecurityManagerFactory(
"classpath:shiro-permission.ini");
SecurityManager securityManager = factory.getInstance();
SecurityUtils.setSecurityManager(securityManager);
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken("jack", "123");
subject.login(token);
boolean authenticated = subject.isAuthenticated();
System.out.println("是否认证成功:"+authenticated);
boolean role1 = subject.hasRole("role1");
System.out.println("role1:"+role1);
boolean allRoles = subject.hasAllRoles(Arrays.asList("role1", "role2"));
System.out.println("role1 + role2:"+allRoles);
boolean permitted = subject.isPermitted("user:create");
System.out.println("user:create:"+permitted);
boolean permittedAll = subject.isPermittedAll("user:create", "user:update");
System.out.println("user:create + user:update:"+permittedAll);
}
}
|
十、使用realm授权
需求
上边的程序通过shiro-permission.ini对权限信息进行静态配置,实际开发中从数据库中获取权限数据。就需要自定义realm,由realm从数据库查询权限数据,realm会根据用户身份查询权限数据,将权限数据返回给authorizer(授权器)。
10.1修改之前realmDemo.java中的doGetAuthorizationInfo方法
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
|
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
String primaryPrincipal = (String)principalCollection.getPrimaryPrincipal();
System.out.println("primaryPrincipal:"+primaryPrincipal);
ArrayList<String> roles = new ArrayList<>();
roles.add("role1");
roles.add("role2");
HashSet<String> permissions = new HashSet<>();
permissions.add("user:add");
permissions.add("user:update");
SimpleAuthorizationInfo simpleAuthorizationInfo = new SimpleAuthorizationInfo();
simpleAuthorizationInfo.addStringPermissions(permissions);
return simpleAuthorizationInfo;
}
|
10.2创建shiro-realm.ini文件,配置自定义的realm,将realm设置到securityManager中,因为之前已经配置过,该步骤可以省略
10.3在AuthorizationDemo中添加方法进行测试
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
|
@Test
public void testAuthorization(){
IniSecurityManagerFactory iniSecurityManagerFactory =
new IniSecurityManagerFactory("classpath:shiro-realm.ini");
SecurityManager securityManager = iniSecurityManagerFactory.getInstance();
SecurityUtils.setSecurityManager(securityManager);
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken("jack","123");
subject.login(token);
boolean authenticated = subject.isAuthenticated();
System.out.println("是否认证成功:"+authenticated);
boolean role1 = subject.hasRole("role1");
System.out.println("role1:"+role1);
boolean allRoles = subject.hasAllRoles(Arrays.asList("role1", "role2"));
System.out.println("role1 + role2:"+allRoles);
boolean permitted = subject.isPermitted("user:create");
System.out.println("user:create:"+permitted);
boolean permittedAll = subject.isPermittedAll("user:create", "user:update");
System.out.println("user:create + user:update:"+permittedAll);
}
|
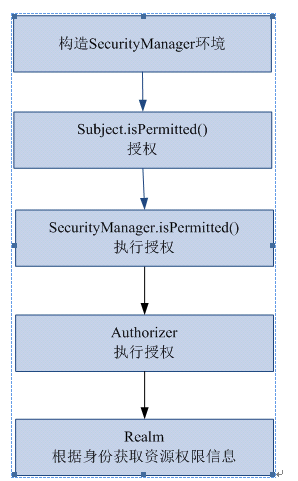
10.4 授权流程
1、对subject进行授权,调用方法isPermitted(“permission串”)
2、SecurityManager执行授权,通过ModularRealmAuthorizer执行授权
3、ModularRealmAuthorizer执行realm(自定义的Realm)从数据库查询权限数据,调用realm的doGetAuthorizationInfo授权方法
4、realm从数据库查询权限数据,返回ModularRealmAuthorizer
5、ModularRealmAuthorizer调用PermissionResolver进行权限串比对
6、如果比对后,isPermitted中"permission串"在realm查询到权限数据中,说明用户访问permission串有权限,否则 没有权限,抛出异常。
十一、SpringBoot整合Shiro
11.1导入依赖
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
| <dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.8.0</version>
</dependency>
<dependency>
<groupId>com.baomidou</groupId>
<artifactId>mybatis-plus-boot-starter</artifactId>
<version>3.5.1</version>
</dependency>
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
</dependency>
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>druid-spring-boot-starter</artifactId>
<version>1.2.8</version>
</dependency>
<dependency>
<groupId>org.projectlombok</groupId>
<artifactId>lombok</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
|
11.2配置application.yml
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
| server:
port: 8081
servlet:
session:
tracking-modes: cookie
spring:
datasource:
username: root
password: root
url: jdbc:mysql://localhost:3306/shiro?serverTimezone=Asia/Shanghai&characterEncoding=utf8
driver-class-name: com.mysql.cj.jdbc.Driver
type: com.alibaba.druid.pool.DruidDataSource
thymeleaf:
cache: false
prefix: classpath:/templates
suffix: .html
encoding: UTF-8
mode: HTML5
servlet:
content-type: text/html
mybatis-plus:
mapper-locations: classpath:mapper/*.xml
configuration:
log-impl: org.apache.ibatis.logging.stdout.StdOutImpl
map-underscore-to-camel-case: true
|
11.3编写ShiroRealm
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| package com.couture.realm;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
public class ShiroRealm extends AuthorizingRealm {
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
return null;
}
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
return null;
}
}
|
11.4编写ShiroConfig
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
| package com.couture.config;
import at.pollux.thymeleaf.shiro.dialect.ShiroDialect;
import com.qf.realm.ShiroRealm;
import org.apache.shiro.mgt.DefaultSecurityManager;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.CookieRememberMeManager;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.apache.shiro.web.servlet.SimpleCookie;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
@Configuration
public class ShiroConfig {
public ShiroRealm getShiroRealm(){
return new ShiroRealm();
}
@Bean
public SecurityManager getSecurityManager(){
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
securityManager.setRealm(getShiroRealm());
return securityManager;
}
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(SecurityManager securityManager){
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager);
shiroFilterFactoryBean.setLoginUrl("/toLogin");
shiroFilterFactoryBean.setUnauthorizedUrl("/refuse");
LinkedHashMap<String, String> map = new LinkedHashMap<>();
map.put("/js/**","anon");
map.put("/css/**","anon");
map.put("/jquery/**","anon");
map.put("/layui/**","anon");
map.put("/login","anon");
map.put("/**","authc");
shiroFilterFactoryBean.setFilterChainDefinitionMap(map);
return shiroFilterFactoryBean;
}
}
|
| 过滤器简称 |
对应的java类 |
| anon |
org.apache.shiro.web.filter.authc.AnonymousFilter |
| authc |
org.apache.shiro.web.filter.authc.FormAuthenticationFilter |
| authcBasic |
org.apache.shiro.web.filter.authc.BasicHttpAuthenticationFilter |
| perms |
org.apache.shiro.web.filter.authz.PermissionsAuthorizationFilter |
| port |
org.apache.shiro.web.filter.authz.PortFilter |
| rest |
org.apache.shiro.web.filter.authz.HttpMethodPermissionFilter |
| roles |
org.apache.shiro.web.filter.authz.RolesAuthorizationFilter |
| ssl |
org.apache.shiro.web.filter.authz.SslFilter |
| user |
org.apache.shiro.web.filter.authc.UserFilter |
| logout |
org.apache.shiro.web.filter.authc.LogoutFilter |
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
| anon:admins
|
anon,authcBasic,authc,user是认证过滤器
perms,roles,ssl,rest,port是授权过滤器
11.5创建controller
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
| package com.couture.controller;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.IncorrectCredentialsException;
import org.apache.shiro.authc.UnknownAccountException;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.subject.Subject;
import org.springframework.stereotype.Controller;
import org.springframework.ui.Model;
import org.springframework.web.bind.annotation.RequestMapping;
@Controller
public class UserController {
@RequestMapping("toLogin")
public String toLgoin(){
System.out.println("toLogin");
return "/login";
}
@RequestMapping("login")
public String login(){
System.out.println("login");
return "/login";
}
@RequestMapping("refuse")
public String refuse(){
System.out.println("refuse");
return "/refuse";
}
@RequestMapping("index")
public String index(){
System.out.println("index");
return "/index";
}
@RequestMapping("add")
public String add(){
System.out.println("add");
return "/add";
}
@RequestMapping("select")
public String select(){
System.out.println("select");
return "/select";
}
@RequestMapping("delete")
public String delete(){
System.out.println("delete");
return "/delete";
}
}
|
启动工程,进行测试
11.6编写对应的login.html页面(以及其他页面)
login.html
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| <!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<center>
<form action="login">
用户名:<input type="text" name="username"><br> <br>
密码:<input type="password" name="password"><br> <br>
<input type="submit" value="登录">
</form>
</center>
</body>
</html>
|
refuse.html
1
2
3
4
5
6
7
8
9
10
| <!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1><font color="red">拒绝访问!!!</font> </h1>
</body>
</html>
|
index.html
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| <!DOCTYPE html>
<html lang="en" xmlns:shiro="http://www.w3.org/1999/xhtml">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>主页面</h1>
<a href="add">添加用户</a>
<a href="select">查询用户</a>
<a href="delete">删除用户</a>
<a href="update">修改用户</a>
<a href="/logout">退出</a>
</body>
</html>
|
add.html
1
2
3
4
5
6
7
8
9
10
| <!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>添加用户</h1>
</body>
</html>
|
select.html
1
2
3
4
5
6
7
8
9
10
| <!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>查询用户</h1>
</body>
</html>
|
delete.html
1
2
3
4
5
6
7
8
9
10
| <!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>删除用户</h1>
</body>
</html>
|
11.7实现用户认证,修改UserController中的login方法
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| @RequestMapping("login")
public String login(String username, String password){
System.out.println("login");
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken(username, password);
subject.login(token);
boolean authenticated = subject.isAuthenticated();
if(authenticated){
return "/index";
}
return "/login";
}
|
11.8修改ShiroRealm中的AuthenticationInfo方法
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| @Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
String principal = (String)token.getPrincipal();
System.out.println(principal);
String credentials = new String((char[])token.getCredentials());
System.out.println(credentials);
if("jack".equals(principal) && "123".equals(credentials)){
return new SimpleAuthenticationInfo(principal,credentials,"ShiroRealm");
}
return null;
}
|
访问路径进行测试即可!
11.9实现用户授权,在ShiroConfig中的shiroFilter方法中添加被授权的信息
1
2
3
|
map.put("/delete","perms[user:delete]");
map.put("/select","perms[user:select]");
|
配置之后重启项目,访问该资源路径时则无法访问,此时需要配置授权信息
11.10修改ShiroRealm中的doGetAuthorizationInfo方法
1
2
3
4
5
6
7
8
9
10
11
12
13
| @Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principals) {
SimpleAuthorizationInfo simpleAuthorizationInfo = new SimpleAuthorizationInfo();
HashSet<String> set = new HashSet<>();
set.add("user:select");
set.add("user:update");
simpleAuthorizationInfo.addStringPermissions(set);
return simpleAuthorizationInfo;
}
|
然后重启项目,再次访问相应授权路径页面
11.11Shiro整合thymleaf标签
1
2
3
4
5
| <dependency>
<groupId>com.github.theborakompanioni</groupId>
<artifactId>thymeleaf-extras-shiro</artifactId>
<version>2.0.0</version>
</dependency>
|
11.12在ShiroConfig中添加该方法
1
2
3
4
| @Bean
public ShiroDialect getShiroDialect(){
return new ShiroDialect();
}
|
11.13修改index.html页面中测试
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
| <!DOCTYPE html>
<html lang="en" xmlns:shiro="http://www.w3.org/1999/xhtml">
<head>
<meta charset="UTF-8">
<title>Title</title>
</head>
<body>
<h1>主页面</h1>
<a href="add">添加用户</a>
<a href="select">查询用户</a>
<a href="delete" shiro:hasPermission="user:delete">删除用户</a>
<a href="update" shiro:hasPermission="user:update">修改用户</a>
<a href="/logout">退出</a>
</body>
</html>
|
启动工程,再次进行测试即可
11.14实现用户退出(两种方式),在相关index.html页面中添加超链接
1
| <a href="/logout">退出</a>
|
11.15在ShiroConfig中的shiroFilter方法中添加退出配置(第一种)
1
2
|
map.put("/logout","logout");
|
11.16在UserController中添加logout方法(第二种)
1
2
3
4
5
6
7
| @RequestMapping("logout")
public String logout(){
System.out.println("logout");
Subject subject = SecurityUtils.getSubject();
subject.logout();
return "/login";
}
|
11.17记住我rememberMe,在login.html页面中添加记住我
1
| <input type="checkbox" name="rememberMe">记住我<br> <br>
|
11.18在UserController中的login方法配置rememberMe参数
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
| @RequestMapping("login")
public String login(String username, String password,boolean rememberMe){
System.out.println("login");
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken(username, password,rememberMe);
subject.login(token);
boolean authenticated = subject.isAuthenticated();
if(authenticated){
return "/index";
}
return "/login";
}
|
11.19在ShiroConfig类中添加相关方法以及代码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
| package com.couture.config;
import at.pollux.thymeleaf.shiro.dialect.ShiroDialect;
import com.qf.realm.ShiroRealm;
import org.apache.shiro.mgt.DefaultSecurityManager;
import org.apache.shiro.mgt.SecurityManager;
import org.apache.shiro.spring.web.ShiroFilterFactoryBean;
import org.apache.shiro.web.mgt.CookieRememberMeManager;
import org.apache.shiro.web.mgt.DefaultWebSecurityManager;
import org.apache.shiro.web.servlet.SimpleCookie;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import java.util.LinkedHashMap;
@Configuration
public class ShiroConfig {
@Bean
public CookieRememberMeManager getCookieRememberMeManager(){
SimpleCookie simpleCookie = new SimpleCookie("renemberMe");
simpleCookie.setMaxAge(3600*24*31);
CookieRememberMeManager cookieRememberMeManager = new CookieRememberMeManager();
cookieRememberMeManager.setCookie(simpleCookie);
return cookieRememberMeManager;
}
public ShiroRealm getShiroRealm(){
return new ShiroRealm();
}
@Bean
public SecurityManager getSecurityManager(){
DefaultWebSecurityManager securityManager = new DefaultWebSecurityManager();
securityManager.setRealm(getShiroRealm());
securityManager.setRememberMeManager(getCookieRememberMeManager());
return securityManager;
}
@Bean
public ShiroDialect getShiroDialect(){
return new ShiroDialect();
}
@Bean
public ShiroFilterFactoryBean getShiroFilterFactoryBean(SecurityManager securityManager){
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager);
shiroFilterFactoryBean.setLoginUrl("/toLogin");
shiroFilterFactoryBean.setUnauthorizedUrl("/refuse");
LinkedHashMap<String, String> map = new LinkedHashMap<>();
map.put("/js/**","anon");
map.put("/css/**","anon");
map.put("/jquery/**","anon");
map.put("/layui/**","anon");
map.put("/login","anon");
map.put("/logout","logout");
map.put("/delete","perms[user:delete]");
map.put("/select","perms[user:select]");
map.put("/index","user");
map.put("/**","authc");
shiroFilterFactoryBean.setFilterChainDefinitionMap(map);
return shiroFilterFactoryBean;
}
}
|
ps:登录页面勾选 记住我 进行测试